Cell phones have become more than just a device used to make and receive calls. Some of us are on our phones every second of every day. You use it for anything from taking photos at the beach to online shopping or depositing checks. Cell phones hold a lot of personal information and the thought of our phones being at risk is certainly horrifying. The unfortunate truth is that mobile devices can be hacked. To make matters worse, the impacts can be life-changing. Phones have some sort of built-in protection, otherwise they wouldn’t make it past phase one of production but don’t let that fool you – installing mobile antivirus onto your cell phone will maximize safety and minimize the risks of a cyberattack, even if you don’t think you need it.
Common Pathways to Mobile Cyberthreats
Mobile devices face plenty of risks just like any device including PCs, desktops, and servers. Since we are on our phones so much, often in public, we tend to face even more risks than with a typical device. Logging onto public WiFi, or taking a chance on an unfamiliar and suspicious website (perhaps you’re hoping it’s not malicious, just poorly designed) might pose a huge threat that can be life changing. Although companies, such as Apple, Samsung and others, have to put safety features in place to sell safe and reliable products, there are still loopholes that cyber attackers will take advantage of. Here are some common ways that mobile devices can get infected.
Downloading apps from unreliable stores
Bigger name app stores, like Apple and Google Play, are more regulated and will scan to make sure apps are safe for consumers. Even so, don’t assume that every app will be safe, as these stores still might have shortfalls (i.e. Sharkbot, discussed later). Apps from other locations entirely might be even more unsafe and will create a vulnerability in your device.
Bad links and redirects
On a smartphone, it can be easy to misclick on an unsafe link with just the tap of your finger. One simple click can invite a virus onto your device.
Suspicious links and attachments in your email or text messages
This is a huge one for mobile devices. Spam messages are only getting more and more powerful and sometimes undetectable. Attackers will use phishing tactics to coerce users into opening a bad attachment or link that will end up harming their phone. Be wary of spam text messages and emails. Never, ever open a link or attachment unless you know it’s from a trustworthy sender. Confirm with them via a phone call, if you must.
Embedded malware in sites or Wi-Fi networks
Sites and networks might ask for your credentials, only to leave behind bad redirect links with dangerous code. Now your device is at risk for some sort of cyber threat.
Public Wi-Fi
While it may seem convenient, connecting to public Wi-Fi networks can actually be extremely perilous. These networks are shared among hundreds or even thousands of devices. The lack of security and the public nature of these Wi-Fi networks is precisely what makes it so easy for hackers to intercept.
Drive-by downloads
Malicious sites can hack your device with drive-by downloads that launch an attack without any action needed from the user. You don’t have to click or open any external files, the code can execute all on its own. Talk about spooky.
Android vs. iOS Mobile Devices
Depending on which operating system or brand you prefer, whether it’s Android or iOS, Apple or Samsung, you might have some different experiences, namely based on the phone’s price, appearance, functions and so on. However, what users don’t particularly ever seem to notice are the different levels of security in these devices. Apple smartphones (iPhones) are “closed source,” while Android devices are “open source.” Source code essentially just refers to the code by which the device is programmed. Closed source code cannot be edited or accessed by the developer or the owner. Open source code, however, can. So Apple users can’t change a thing about the settings embedded in the source code, while Android users can.
But what does this mean for security? Since open source code is accessible by the owner and other actors, most consider this to be less safe. Users can modify the default settings that Android developers provide, even those settings meant to maximize the security of your device. The owner can change these settings, and even if they don’t intend to, the devices are still quite fragile and more prone to malware. We point this out because it is something for users to be aware of and another reason why antivirus software can be of good use, especially for our Android friends.
Can iPhones get Viruses?
This difference between open source and closed source code for Apple and Android devices might make users think iPhones are invincible. Many still hold that belief, despite it having been disproven. Apple designed their system in such a way that each app runs in a separate virtual space. Viruses are contagious. They spread on devices by communicating with other programs, so once it hits one app, it can move onto the others. It’s like staying home from work when you know you’re sick – this will prevent you from infecting others. Because Apple separates where the apps run, they won’t end up spreading the virus to another app. This prevents a virus from overtaking your iPhone.
What about those rare cases where an iPhone is hacked? Here’s a brief note about a concept known as “jailbreaking” from the cybersecurity company Kaspersky:
The point is: any smartphone can get infected, including iPhones. Viruses and malware are possible threats to any mobile device, even those from the most reputable companies, with the maximum protection. Whether you have an Android, a Windows phone (we know there’s still some of you out there, even if you’re not in the majority 😜) or an iPhone, or yet another type of smartphone, the threats still exist.
Some Sources Claim, “What’s There is Enough..”
Your mobile device has some layers of protection to prevent hackers from trying to infiltrate your phone. For example, with the Google Play Store, Android offers Google Play Protect to scan apps for malicious activity. When you search the web, you’ll probably receive some sort of redirect that tells you the link is “bad” or “not trusted” by Google. This is your phone’s attempt to protect and prevent you from accessing a malicious link.
If you browse the web for whether or not you need additional antivirus software on top of whatever your phone offers, a lot of sources might say no. They claim it’s “repetitive” or simply “unnecessary.” Yes, this can be true, if you get the wrong antivirus software. Take what Android has installed, as an example. Google Play Protect is a built-in defense against malware that scans apps in the Play Store before users download them. Play Protect works beyond just the Play Store and acts as a pseudo antivirus for your Android but don’t be fooled. Just because Play Protect exists doesn’t mean it covers every single vulnerability that your device might face. After all, having an extra layer of antivirus from a reputable security technology company will always be the better choice.

Updates, Updates, Updates
Another important measure that the majority of modern-day smartphones offer is frequent updates. These come around once every month or once every several months perhaps. Some of these updates will create major changes for phone users, possibly changing the entire appearance of your phone, but that’s not always the case. Take Apple’s transformation from iOS (iPhone Operating System) 6 to iOS 7 for example, which completely transformed the old user interface (UI) into a more modern look. Since then, Apple has made additional adjustments to its appearance. These shifts were visible to users, so most people updated right away.
But updates are more than just UI changes or new emojis. Most developers come out with updates pretty frequently to fix any bugs or glitches, patch any previously overseen security vulnerabilities, and overall, to make improvements to their systems. By updating, your mobile device will likely run faster, remain compatible with newer apps, and even look more aesthetically pleasing but most importantly, you will continue to protect yourself from any potential vulnerabilities that developers may have overlooked in the last version of your OS. Frequent updates are a must for any device, and updating apps is just as important as updating your operating systems. When users forget or neglect to update their device as soon as a new version comes out, they may be putting their device at a huge risk.
So where does this fit in? Well, updates are just another way phone companies try to keep your device safe but like we mentioned, nothing is foolproof. Updates are not the be-all and end-all to security. Utilizing mobile antivirus, on top of good mobile device management practices, will ensure that your data is always protected.
⚠️ Not All Mobile Antivirus Software Is Created Equal!
So you might be considering downloading and installing a mobile antivirus software onto your device, which we highly recommend. However, be careful, as not any mobile “antivirus” will be sufficient or even safe. Some developers will actually create fake applications that appear to fight viruses but actually are viral (more to come on this later). Instead of allegedly protecting a mobile device, these sorts of apps will actually enable the app creator to carry out a variety of malicious actions. This could include spreading bad links (phishing) to others, or downloading viruses, or worse, malware onto your device. They might try to steal or even change your banking information through your mobile device, and have the ability to access passwords and log in credentials. You and your device could face even more of a risk when it comes to a possible data breach, identity theft, financial corruption and more.
Sharkbot Dropper on Android
A recent example of a fake mobile antivirus “solution” was floating around the Google Play Store back in early 2022. Check Point Researchers encountered several applications that appeared as if they were legitimate antivirus solutions. When users downloaded these apps, they would actually install an Android Stealer called Sharkbot, which would actually steal credentials and banking information. Researchers discovered that Sharkbot Dropper was running in 4 applications on Google Play and immediately notified Google. Within less than a week, the apps were removed from the Google Play store. Days and days following, a few more droppers were also discovered in the store and effectively removed soon after. Still, even with Google’s quick response time, it never seems to be quick enough. These apps were still downloaded and installed about 15 thousand times. It likely impacted many people in some capacity. Two apps that contained the Sharkbot malware on the Google Play Store, went by the names “Mister Phone Cleaner,” and “Kylhavy Mobile Security.”
One assumes that they’ll be safer off when downloading an antivirus app but instead, their device could be in even greater danger than before. Unfortunately, this is an easy mistake to make when users don’t understand or don’t conduct enough research about the apps they’re downloading. You might be asking: How do malicious apps like these even make it to the app store in the first place? Good question.
The Danger of Mobile Applications
Are mobile apps unsafe and does mobile antivirus do anything to protect you from potentially threatening applications? As seen with the fake antivirus apps that actually installed Sharkbot, not all apps can be trusted. Because of the sheer number of apps being pushed through app stores like Google Play everyday, malware can sometimes sneak through. A trojan horse is a type of malware that seems like legitimate code or software but is actually viral. These will often make their way onto phones via apps. While app stores like Google Play have some built-in measures like Play Protect to safeguard users, it’s clear that it isn’t entirely perfect, or works as intended 100% of the time. Take Sharkbot – apps with this virus made it past inspection, onto the app store, and right onto devices.
As with your OS, frequent app updates will prevent dangerous shortcomings in apps from harming your phone and your data. Bugs, glitches, and possible security risks are just a few things that developers will fix as part of their released updates. Phones might allow you to turn on automatic updates for apps; this way, when the developers release a new version, you don’t need to worry about downloading it. But another thing to be mindful of, and what’s especially critical in the beginning, is to get familiar with the app developer before you download anything from them. Avoid downloading apps by no-name developers and stick with big-name trusted brands instead. Not all apps made by individual developers are bad but unless you’re willing to do the research, the safest bet is to stick with companies that have already built their reputation over decades; the ones that’ll easily come up in a Google search, for instance.
Mobile Privacy and Security
When you download an app on your phone, you might be allowing it to do and see more than you would like, and more than is actually necessary for the functionality of the application. Misreading privacy policies, app guidelines, and app permissions might mean giving developers access to a lot more than you think. When you download an app from a verified app store, it will likely prompt you to grant access to certain sensitive permissions. This includes phone contacts, camera, microphone, photos, location and more. Before you click “OK” or “allow,” take a moment to consider the level of access they’re requesting. Does a music app really need to access my camera? Do you want a third-party messenger to see all of your photos? Take app permissions seriously; at the end of the day, the user is responsible for making these choices. Unfortunately with many apps, there are misconceptions about how developers collect, see, and even use your data. It’s wise to just be aware of this and recognize the possible ways the companies might be analyzing or even selling your personal information. Scary, right? Also consider what would happen if those app developer companies encountered a cyber attack; are they prepared to protect your data? Do they have the correct security measures in place? Question everything.
Apps Can Be Fishy…
While a part of security lies in the hands of the consumers, another part belongs to the transparency of developers. A lot of apps may be out front and tell users, “Hey, we’re gonna track your data, is it okay if we share it with our developers to strengthen our app?” You might choose yes or no, depending on whether or not you want to share your usage with developers. There are plenty of apps out there that make it onto trusted app stores and become well-known, but all in all, aren’t what we think they are. For example, a lot of health and tracking apps seem to misuse personal data. Replika AI, for example, is an artificial intelligence (AI) chatbot that users can interact with. The app is a little bit creepy, as a bot is trying to replicate a human being, perhaps even being manipulative at times. This app could be dangerous especially for kids who may not understand the potential of digital manipulation. Talkspace, BetterHelp, and Happify are three apps that prompt users with questionnaires before disclosing their privacy policy. Crazy, huh?

App to Malware Gateway
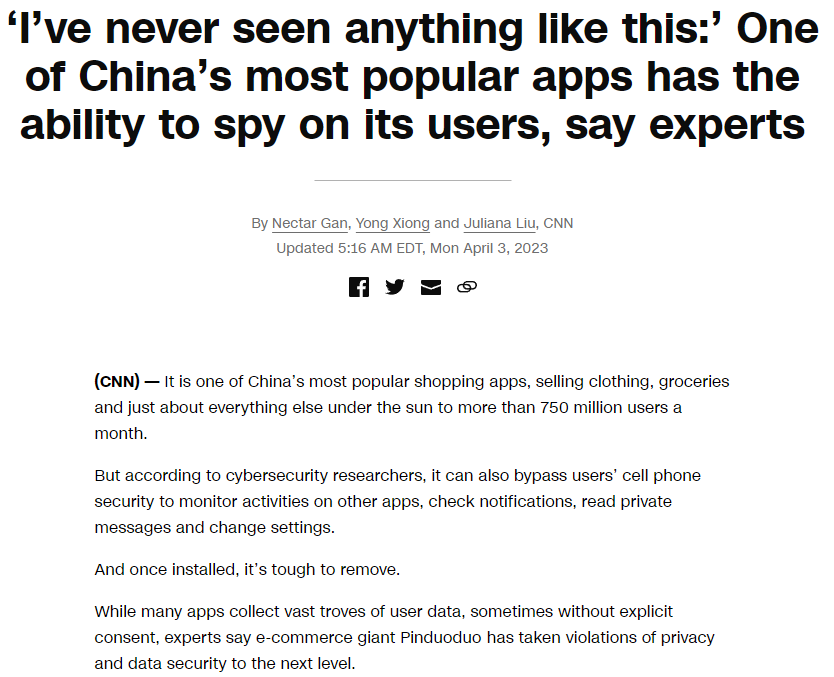
One of the ways malware could find its way onto your device is through an unsafe app. While a lot of apps are safe, malevolent apps still exist. For example, in March 2023, Google Play suspended users from downloading Pinduoduo, a Chinese app that posed major security concerns. Pinduoduo, owned by PDD Holdings Inc, is a Chinese e-commerce platform. As more and more users started downloading the app, researchers found malware in certain versions of the app. Google Play was successful in being able to monitor the app for its harmful behavior, thus blocking attempts to install the malicious app altogether. Google immediately warned users of the questionable nature of the app, and urged users to uninstall it immediately from their devices. Temu, Pinduoduo’s sister app, is another shopping and commerce app. Officials suspect that this is potentially subject to the same malware as Pinduoduo. Once malware like this gets installed, it is extremely difficult to remove, which is all the more reason why antivirus software is critical for mobile devices. Pinduoduo’s malware was said to be incredibly sophisticated.
“We haven’t seen a mainstream app like this trying to escalate their privileges to gain access to things that they’re not supposed to gain access to,” said Mikko Hyppönen, chief research officer at WithSecure, a Finnish cybersecurity firm.
Reported by CNN
How Do Malicious Apps Bypass Security Controls?
Although Google Play uses Play Protect to prevent malicious apps from sneaking into the store, some threat actors are using techniques to leverage their way onto the platform regardless. Google states that they, “thoroughly evaluate apps on the Google Play Store,” and they estimate that less than 1% of Google Play app downloads are what they consider Potentially Harmful Applications (PHAs). How do apps make their way into that 1%? Google’s Cybersecurity Actions Team released in their July 2023 Threat Horizons Report that apps were, “evading cloud enterprise detection through versioning.” Simply put, versioning is when an app passes the initial security check by Google but later on, a software update changes the code to create a malicious version of the app. Dynamic code loading (DCL) is a common versioning tactic, which is an app that downloads and uses code files from untrustworthy sources.
Researchers at software company ESET detected a trojan app called iRecorder – Screen Recorder on the Google Play store. The app made its way onto the store using versioning – it didn’t show any harm initially but after a few months, the developers implemented malicious code into an update. iRecorder would extract microphone recordings and steal files, without the permission of users, suggesting that there was possible involvement in an espionage campaign. Google removed the app – which had more than 50,000 downloads – from their store after hearing about ESET’s research.
Google recommends that users remain vigilant about the apps that they download and that they always keep their devices up-to-date. Luckily, the company is very transparent about threats you could face, and users can learn more about this in the Google Transparency Report under the Play Store Safety section.
The Best Ways to Protect your Device
So, now what? How do we know what is safe to download on our phones? How do we protect our small yet so highly treasured devices, that contain within them just about everything we need in our lives – from photos and memories to important financial information and documents?
Beyond antivirus, practicing good mobile device management habits and being vigilant will help make your phone more secure.
Here Are Some Helpful Tips to Keep Your Device Safe
#1: Be cautious when downloading files and attachments.
We cannot stress this enough. Be mindful of the website you’re downloading attachments from and pay attention to both the developer and the privacy policies of apps on the app store.
#2: Only open links from a trustworthy sender
Always double check that they’re legitimate. Don’t fall for a hacker’s social engineering tactics!
#3: Use strong passwords for accounts on your device.
Have a good passcode/PIN to get into the phone itself and THEN, create a different PIN entirely, meant specifically for financial apps. This way, even if someone knows the PIN to access your phone, it won’t give them the keys to the kingdom and the ability to also compromise your finances.
#4: Regularly update your phone.
Many phones will allow you to update overnight (as long as your phone is connected to power), so that you can avoid interruptions.
#5: Only use secure Wi-Fi.
Public Wi-Fi can be unpredictable and anyone can intercept it; this puts information on your phone at risk.
#6: Watch out for spam and phishing messages.
Be aware of what they might look like. Refer to our article for some examples of possible spam text messages.
#7: Be careful with apps and weary of their privacy/security policies.
They might be trying to find some loopholes that indicate that they’re misusing your personal data.
Having an extra level of security in addition to these safe practices will further optimize your mobile protection.
The Best Free Antivirus for Android or iPhone Mobile
You may be wondering what’s the best free antivirus for android or iPhone mobile but the reality is reflected in the old adage: “You get what you pay for.” Free software usually isn’t going to be the best, and it could come with a price, such as loss of privacy, data shared with third parties and more. You won’t know until you check but the antivirus that we recommend isn’t going to be a free one—it’s going to be one that’s effective, made by a reputable company and is known for it’s reliability, just as it should be. So, instead of wondering what’s the best free mobile antivirus, instead you should ask yourself: “What’s the best mobile antivirus?” Now you’ve got your priorities straight.
6 Reasons Why Having Antivirus Software for Your Phone Is Essential
#1: Cyberattacks are all the more likely nowadays.
Don’t take any risks by not protecting your phone.
#2: Our phones have a lot of data.
You don’t want to lose or threaten personal, confidential information. How would you feel if one day, it was just out there, on the worldwide web?
#3: Apps and sites can be misleading.
As we’ve learned, apps can have malware themselves.
#4: One click, it can all be over.
It’s easy to accidentally click on a pop-up or link with a slippery finger.
This can end up downloading malware on your device if you don’t have the right protection.
#5: Spam happens.
Antivirus does its job to protect you from junk emails with fake links.
#6: A phone’s built-in security from the manufacturer may not be enough.
#7: It’ll make you look so impressive 😉
Here’s a bonus tip: You’ll get to impress your boss and/or all of your friends who haven’t yet caught onto the mobile device security train. Maybe you can educate them on why it’s necessary and teach them something new.
Trend Micro Antivirus for Mobile Device Security
Here at Computero, we trust Trend Micro with all of our business-grade antivirus software needs. They offer the utmost comprehensive protection, complete checks, and overall, the best security for your network and devices. Trend Micro’s Mobile Security software is a reliable option available for both Android and Apple iPhone devices. It protects you against potentially harmful websites, malicious apps, ransomware, unsafe WiFi networks and more.