By Mary Grlic
Email is a common communication mode used for business and personal interactions. A lot of us tend to send information over email, like finances, passwords, login credentials, health data, and bank account numbers for a number of reasons. It’s convenient, easy to use, quick, and relatively “safe.” Whenever we are sending emails, however, it is important to encrypt data in order to prevent outside actors from gaining unauthorized access. Encryption is a useful tool that can help you protect any messages sent through email. When using trusted mail services, there is already a safety factor when sending emails. However, for extra protection, encrypting emails is a good idea to make sure you send secure emails in Google, Outlook, and other mail services.
What does Encryption Mean?
Encryption is a way of scrambling data so that only authorized users can understand and access the information. Technically, encryption involves translating human “plaintext” to incomprehensible code known as ciphertext. The text is put into random order to make sure outside interceptors cannot understand it. To decrypt a message, users will need to know the code, which is the set of characters to decode the encrypted data. When users encrypt an email, they actively protect the message and its contents from interception or unauthorized access.
Why encrypt?
Encryption ensures the maximum security of your messages. While emails travel through the internet, hackers may be able to intercept the data packets and access the content within the message. With so many hackers ready to attack at any time, it is so important to encrypt your messages to protect them from interception. Billions of unencrypted messages are sent and received daily, making them susceptible to eavesdropping. It’s important to know how to send secure emails to best protect any information in these messages.
What might you need to encrypt?
When sending confidential or personal information through the internet, it is especially important to encrypt your messages and send secure emails. You should not send any private information via email, such as your social security number, because outside organizations would be able to see this data. This will threaten your data security and put you at a major risk. You must encrypt any personal identification and confidential business properties, but always be cautious when sending messages via email. Email encryption is particularly important for industries that deal with sensitive data, like medical records or financial information. An example is healthcare services that follow HIPAA, which may benefit from the security measures provided with Google Workspace for healthcare organizations.
It’s important that every email sent is encrypted, not just the ones that have private information in them. If a hacker was to see that some messages were encrypted while others weren’t, it might raise some alarm bells. It might make your inbox even less secure, as they will be able to access some messages that could lead to unauthorized access.
Are emails already protected?
Transport Layer Security (TLS) is a basic form of encryption that ensures security over email. TLS encrypts data to ensure privacy across the web. As long as the recipient you are emailing uses a mail service provider that also supports TLS, this service will protect your emails. Most major mail providers, like Gmail and Outlook, support TLS. However, if the user you are messaging does not have a mail server that supports TLS, your messages will not be encrypted. This means that any user can gain access to contents within the email at any point of transport. With platforms like Google Workspace, users can choose to only use TLS for incoming and outgoing emails.
End-to-end encryption means that the service provider itself does not have any access to your emails during the transmission process. The only user who can see your messages is the recipient(s) of that email. End-to-end encryption does not guarantee the protection of your emails and their contents. Major mail services can scan your messages for spam and phishing, as well as create convenient auto-reply messages based on the contents of the email.
TLS is not the end-all, be-all security marker. While it is secure, you still must be careful when sending messages through email to ensure that no unauthorized users access private data.
Confidential Mode: is it the same as encryption?
If you want to protect sensitive information via Gmail, you can toggle “confidential mode” on your email. Confidential mode will prevent unauthorized users from getting the message. Note that sending emails in “confidential mode” is not the same as encrypting emails. With confidential mode, you can set an expiration date for the message, meaning the recipient will not be able to access it after a set period. Confidential mode also revokes the ability to forward, copy, print, or download the email. However, recipients can still screenshot or photograph the message. Malicious software can override confidential mode and allow users to save or download attachments as well.
There is an option for senders to lock the confidential email. Recipients will not have access to the message without entering the second layer of security. Confidential mode is an added security measure but may provide a false sense of protection, so be cautious when utilizing confidential mode.
To send emails in Gmail confidential mode:
- Go to Gmail
- Click the icon to “Compose”
- In the bottom right corner of the window, turn on “Confidential Mode” by clicking on the
icon
- In confidential mode, the sender can modify the following expiration date of the message and choose to create an SMS passcode for the email
Turning on confidential mode in Google’s interface
To remove access from a confidential message:
- Go to Gmail
- On the left of the window, click “Sent”
- Open the confidential email you previously sent
- Click “Remove access”
Opening messages sent in confidential mode:
- Recipients can access the messages and their attachments until it expires or until the sender removes access
- Recipients cannot copy, paste, download, forward, or print the email and its attachments
- Recipients may need a password, sent via SMS
Protecting your emails with email encryption
The two main methods of email encryption protocol are S/MIME AND PGP/MIME. Depending on your email provider and type of service you have, you might use a different type of encryption protocol to protect your emails.
S/MIME
Secure/Multipurpose Internet Mail Extensions (S/MIME) is a widely accepted protocol used to send encrypted messages. It is supported by certain editions of Gmail, Outlook, and on iOS devices. This service encrypts messages and can make digital signatures to verify the sender’s identity.
S/MIME encrypts emails with user-specific keys to protect messages during both transmission and delivery. The recipient must receive and then decode the message. S/MIME only works if both users protect their messages with a service that supports it. Additionally, both the recipient and the sender must share the code in advance. Similar to TLS, it does not protect the message once it has received its destination. Your provider can still review the message to place into the “spam” pile or create an auto-reply, making it not entirely encrypted once it reaches its destination.
S/MIME has centralized authority, meaning that it is controlled by the email service itself rather than a third-party organization. It is built into large web-based email companies like Outlook and Google Mail.
Pretty Good Privacy: PGP/MIME
Pretty Good Privacy/Multipurpose Internet Mail Extensions (PGP/MIME) is a security program for email encryption and decryption. It is supported by email providers like Yahoo, AOL, and Android devices. By going through several levels of coding and decoding, PGP/MIME is a great way to protect your messages. PGP uses a three-step process:
- PGP generates a random session key. Users cannot guess this key. The key expires after one use.
- The session key is encrypted using the public key of the intended recipient of the message. The public key is associated with one person’s identity so anyone can use it to send the message.
- The sender sends their encrypted PGP session key and the recipient decrypts the message with their private key. The recipient then uses the session key to decode the actual message.
People can use PGP to encrypt emails and verify digital signatures. Users can use PGP to encrypt files and attachments, and overall, protect their digital footprint. If a user is not sure of another user’s identity, they might also want to include a digital signature that must be decoded.
PGP is a great way to protect and encrypt emails, but there are some disadvantages in everyday use. PGP is difficult to use; encryption with PGP takes time and effort, which can make it complicated for some users. They also must fully understand how to use PGP or else it will not work correctly. Similar to TLS and S/MIME, both users must enable PGP so that it works properly. Third-party PGPs may not be ideal, but they do get the job done when it comes to encryption and digital safety. You will need to download external software to encrypt your messages using PGP.
PGPs for Google and Microsoft
FlowCrypt is a browser plug-in that can be downloaded on the Chrome web store for Gmail end-to-end encryption. With FlowCrypt, users can add “Secure Compose” to their email so that they can easily encrypt emails with just a click of a button. FlowCrypt is easy to set up, allows users to send and receive encrypted emails and attachments, and creates digital signatures.
Similarly, for Outlook 2010-2019, gpg4o is a Microsoft PGP add-on. This service uses OpenPGP encryption through GnuPG (GPG) and operates like other PGPs. Users will have a session key that consists of a public and private key to access the encrypted messages. Using a private key, senders and recipients can decrypt the contents. Users can get gpg4o in the download center. Compatible devices must have Microsoft Outlook 2010 or later and a version of GnuPG v1.4.21 or higher. If they do not have this software, the installation process will guide users through downloading and installing this software. There is a free license available for non-commercial users as well.
How to Encrypt Email in Gmail
In the Google world, S/MIME is only available for paid Google Workspace and GSuite accounts. It only works when both parties have it enabled. To enable S/MIME encryption, follow Google’s instructions here. If your email plan does not allow for S/MIME encryption, PGP will work, so follow the instructions above about downloading and installing a PGP browser extension. Be wary that TLS only goes so far, especially if you are handling client information, personal data, and other sensitive contents via email.
How to Encrypt Email in Microsoft
Similar to Google, S/MIME is only available for specific account plans. You can enable S/MIME by following the instructions from Microsoft here. If your plan doesn’t include S/MIME, using a PGP here will help your information stay safe again.
How to Encrypt for Mobile Phones
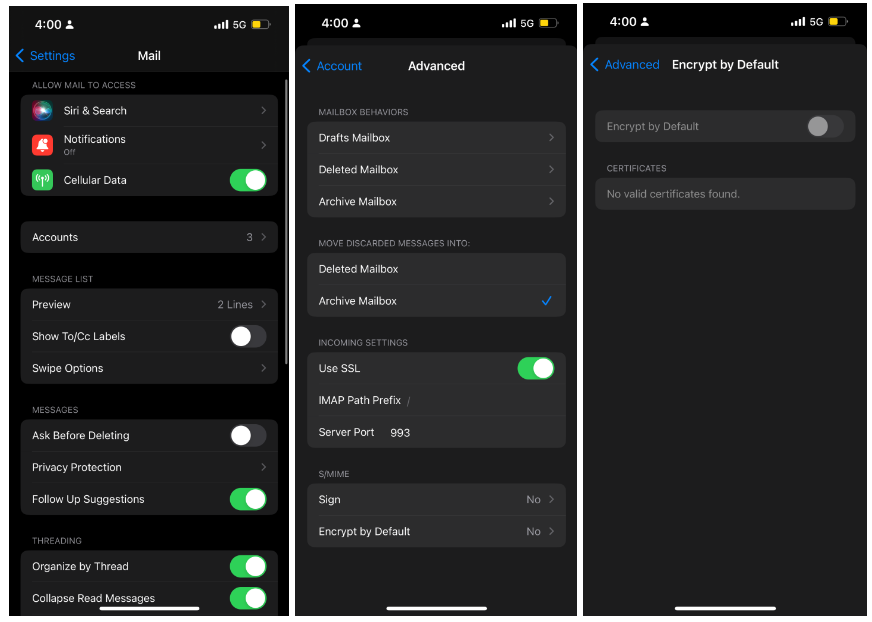
S/MIME is supported on the default Mail app for iOS devices. However, it’s only available if your email provider permits S/MIME and when you have installed the recipient’s certificate, meaning that iOS also knows that they have S/MIME encryption for their messages.
First, go to the Settings app on your iOS device and click into Mail. Then access your accounts and choose the email you want to send an encrypted message with. Click into the account again and go to Advanced settings. On the bottom, there will be a small menu for S/MIME, where you will click on “Encrypt by Default.”
For Android devices, there are a few options involving external apps, like CipherMail app and OpenKeychain. These are examples of PGP protection.
How to Encrypt Email in Yahoo, AOL
To encrypt in Yahoo or AOL, you must use a third-party PGP extension. One example is Mailvelope, which is compatible with Gmail, Microsoft, and Yahoo.





0 Comments