The Health Care Cybersecurity Act of 2026 is a proposed U.S. legislation aiming to strengthen the digital defense of the healthcare sector. It aims to improve cybersecurity preparedness across provider organizations throughout the healthcare industry, with a focus on rural and independent practices, which might lack a dedicated IT team. With the help of IT Health Services, even small and rural healthcare practices can implement strong cybersecurity measures and stay compliant with modern HIPAA standards.
What is HIPAA?
HIPAA (Health Insurance Portability and Accountability Act) is a U.S. law that protects patient health information and ensures data privacy in healthcare.
HIPAA isn’t new, but how it’s enforced and updated is changing to match today’s threats better.
In simple terms, the focus is shifting toward stronger, more practical security measures like:
- Using multi-factor authentication, not just passwords
- Keeping a closer eye on system activity and access
- Regularly checking for risks and vulnerabilities
- Making sure third-party vendors are also secure
This isn’t just about ticking boxes; it’s about actually preventing breaches before they happen.
Driven by rising ransomware attacks, data breaches, and evolving digital healthcare systems, the U.S. Department of Health and Human Services (HHS) is modernizing HIPAA to enforce stricter safeguards for electronic Protected Health Information (ePHI).
For healthcare organizations, this is not just a regulatory update; it’s a mandatory shift from flexible compliance to enforced cybersecurity accountability.
What is the purpose of HIPAA?
The purpose of HIPAA was to make sure employees could continue to receive health insurance coverage when they were between jobs and would not be discriminated against for pre-existing conditions.
The costs would be incurred by health plans and concerns, which might be passed on to plan members and employers.
What does HIPAA consist of?
HIPAA consists of rules that work together to set standards for patient privacy, breach response, and consistent data exchange. The components include:
- HIPAA Privacy Rule: Governs how patient information can be used and disclosed.
- HIPAA Security Rule: The security rule requires covered entities to set requirements for safeguarding PHI via physical and technical safeguards.
- HIPAA Breach Notification Rule: It mandates reporting procedures when PHI is compromised.
- HIPAA Transactions Rule: It standardizes electronic healthcare transactions for accuracy and efficiency.
- HIPAA Unique Identifiers Rule: It establishes uniform identifiers for employers and health plans to streamline data exchange.
Health Care Cybersecurity Act 2025 Explained
This upcoming law is designed to help healthcare organizations improve their cybersecurity, especially smaller practices that may not have big IT teams.
It’s expected to:
- Provide guidance and support for better security practices
- Improve how organizations respond to cyber incidents
- Encourage stronger collaboration across the healthcare system
In short, it’s about making the entire healthcare ecosystem more secure and prepared.
Which best describes the HIPAA Security Rule?
The HIPAA Security Rule is best described as a set of national standards designed to protect electronic protected health information (ePHI). We have listed down the HIPAA Security Rule checklist:
1- Administrative Safeguards
This refers to policies and procedures that are designed to show how the entity will comply with HIPAA.
- Conduct risk assessments
- Introduce a risk management policy
- Restrict third-party access to ePHI
- Test the contingency plan
- Provide employee training on cybersecurity
- Report security incidents
2- Physical Safeguards
Physical safeguards focus on securing devices like laptops and mobile devices. Workstations and data centres where ePHI is stored are liable under HIPAA’s physical safeguards.
- Create policies for the use and positioning of workstations
- Create policies and procedures for the use of mobile devices
- Implement facility access controls
3- Technical Safeguards
Technical safeguards are related to technology that is used to protect and access ePHI.
- Implement access control measures
- Introduce activity logs and audit controls
- Use a mechanism to authenticate ePHI
- Implement a tool for automatic log-off of devices
Why Smaller Practices Should Pay Attention?
A lot of smaller clinics assume they’re too small to be targeted but that’s exactly why attackers go after them.
Common issues we see:
- Outdated systems
- Weak passwords or shared logins
- No proper backup plan
- Limited security awareness among staff
The reality is, one breach can disrupt operations, damage trust, and lead to serious compliance issues.
Why HIPAA is important in healthcare?
HIPAA is vital because it protects patients’ information, builds trust, and makes sure healthcare organizations handle data responsibly.
Protects Patient Privacy
HIPAA safeguards PHI like:
- Medical records
- Test results
- Insurance details
Prevents Data Cyber Threats
HIPAA enforces:
- Encryption
- Access controls
- Security risk assessments
Builds Patient Trust
Patients are likely to:
- Share accurate medical information
- Timely treatment
Ensures Legal Compliance
HPPA sets rules for healthcare providers and vendors.
- Non-compliance can lead to heavy fines
- Firms should follow security standards
Worried About HIPAA Compliance in 2026?
Upgrade to comprehensive healthcare cybersecurity built for today’s risks.
What is HIPAA protected health information?
HIPAA Protected Health Information (PHI) is defined as any health-related data that can identify an individual and is created or shared by healthcare providers or their partners.
What counts as PHI?
PHI includes any of the information related to a person’s:
- Medical condition
- Healthcare services
- Payment details
Examples of PHI
Below are some examples:
- Doctor’s reports
- Health insurance details
- Prescription history
- Appointment records
- Medical bills
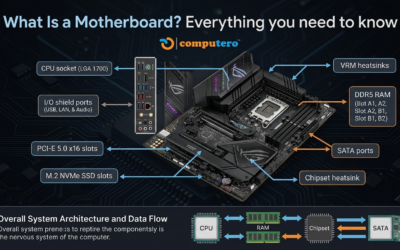
Technology Every Medical Office Should Have
No matter the size of your practice, there are a few basics that should always be in place. Many of these are part of a broader healthcare IT support designed to keep patient data secure and compliant.
Multi-Factor Authentication (MFA)
Adds an extra layer of protection beyond just a password.
Secure Backups
So your data is safe even if something goes wrong.
Endpoint Protection (EDR)
Helps detect and stop threats on computers and devices.
Email Security
Because phishing emails are still one of the biggest risks.
Cloud Security
Ensures patient data is stored and accessed safely.
Regular Security Checks
So you can catch issues early instead of reacting later.
What’s the Future of Healthcare Cybersecurity?
Protecting healthcare data from cyber threats will get more difficult in the future, so security will become a top priority. The risk environment is changing rapidly, which is why it is crucial to identify reliable technology partners and advisors who can help extend your security capabilities.
Besides that, most organizations would require outsourcing a part of their cybersecurity defense planning implementation, monitoring, and management due to the lack of cybersecurity staff.
Discover the reason why Computero is the first choice for global hospital and health system cybersecurity leaders. Visit Computero Now!
Key Takeaways
The Health Care Cybersecurity Act of 2026 is really a major change in the health care sector. With cyber threats increasing not only in scale but also in sophistication, securing patient data (PHI) should not be considered as a mere option anymore; it has become a requirement linked to patient safety and trust.
FAQs
1- What is the best cybersecurity solution for healthcare organizations?
Each organization has different needs and requires different solutions. For example, large health systems looking to reduce their vendor blueprint can consider Computero with just a few vendors.
2- What are the top 5 cybersecurity threats in healthcare?
Top 5 threats include ransomware, phishing, medical device vulnerabilities, and third-party breaches.
3- What is the Health Care Cybersecurity Act?
The Healthcare Cybersecurity Act protects firms from cyber attacks and makes sure there is availability of medical services and the integrity of compliance.
4- What is the role of cybersecurity in healthcare?
Cybersecurity in healthcare is vital for protecting patients’ safety, maintaining data privacy, and ensuring the continuity of medical services.